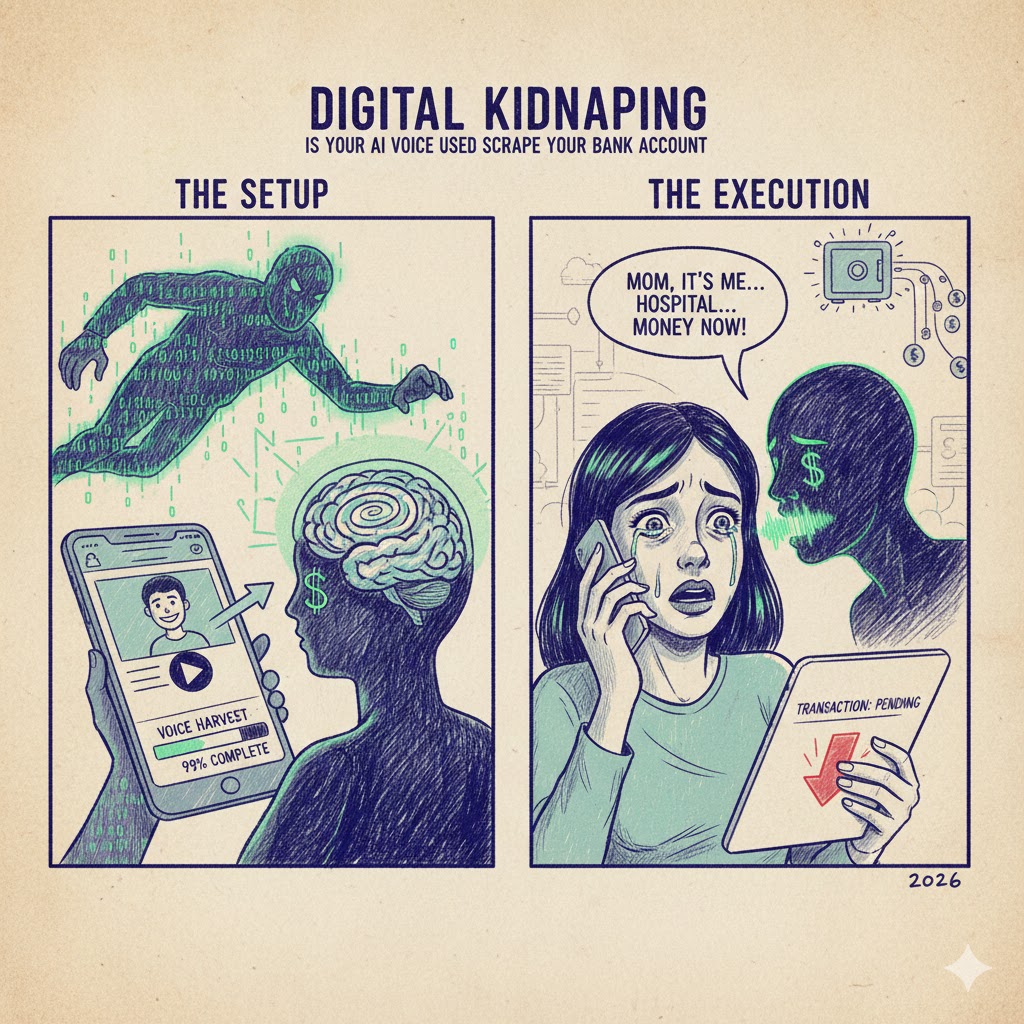
Imagine your phone rings at 2:00 AM. The caller ID displays your daughter’s name. You pick up, and you hear her—the exact pitch, the familiar stutter when she’s scared, the frantic breathing. She screams, “Dad, I’ve been in a terrible accident! I’m at the hospital, and they won’t treat me unless I pay the deposit right now. Please, I’m sending a link, just authorize it!”
Your heart drops. You don’t think. You don’t check. You click. Ten minutes later, you find out your daughter was fast asleep in her dormitory. The person on the phone wasn’t your child—it was a Generative AI Clone programmed to steal your life savings.
Welcome to 2026, the era of Digital Kidnapping.
The Evolution of the “Perfect Crime”

In the past, hackers needed your password or your physical credit card. Today, they only need 30 seconds of your voice. If you have ever posted an Instagram Reel, a TikTok, or a LinkedIn video, you have already handed over the keys to your vault.
AI Voice Cloning tools like ElevenLabs and VASA-1 have reached a point where they can mimic human emotion, sarcasm, and even regional accents with 99% accuracy. This isn’t just “imitation”; it’s a digital bypass of the most fundamental human sense: The sense of sound.
My Personal Nightmare: When I Met “My Digital Ghost”

I want to share something I’ve never written about publicly before. Last year, I was experimenting with high-end voice synthesis to automate my YouTube narration. I trained a model on three hours of my own speech. It was perfect. Too perfect.
A week later, my close business partner messaged me: “Hey, why did you sound so weird on the phone today? And why did you need the admin credentials for the server again?” My blood ran cold. I hadn’t called him. Someone had scraped my voice from a public interview I gave, used an AI “wrapper” to call my partner, and attempted to social-engineer their way into our database. The AI-me even laughed at a joke my partner made. It knew how I laughed.
That moment changed my perspective forever. I realized that my voice—the thing that defines me—was now a weapon that could be fired at my own friends. This experience is exactly why I became obsessed with digital hygiene. If you are worried about your voice being used against you, you need to audit your digital footprint. I always point my colleagues toward CybrTools to learn how to lock down personal data before it’s too late.
How the “Scrape” Actually Happens

The process is terrifyingly professional. Hackers don’t just guess; they execute a four-stage operation:
- The Audio Harvest: They use bots to scrape audio from your social media profiles.
- The Social Map: They identify your “High-Value Targets”—your parents, your spouse, or your boss—using your public “Following” list.
- The Scripting: They use LLMs (like a dark version of ChatGPT) to write a high-pressure script that triggers “Fight or Flight” responses.
- The Bank Bypass: Many modern banking apps use “Voice ID” for login. The AI clone simply calls the bank’s automated line and “talks” its way into your account.
The Psychological Trap

The reason Digital Kidnapping works so well isn’t because the tech is perfect; it’s because the psychology is exploited. When we hear a loved one in pain, our “Prefrontal Cortex” (the logical part of the brain) shuts down. We enter a state of emotional urgency. Hackers know that if they can keep you on the phone for 5 minutes, they have already won.
To counter this, you need more than just a strong password. You need a “Human Firewall.” For those looking for technical ways to encrypt their communications and stay ahead of these scams, checking out the resources at CybrTools is a mandatory first step in modern cybersecurity.
How to Protect Your Family (The “Safe-Word” Strategy)

Since we can no longer trust our ears, we must trust “Shared Secrets.” Here is the 2026 survival guide for your family:
- The Family Code Word: Establish a secret word (e.g., “Blue Pineapple”) that is never written online. If anyone calls claiming an emergency, they must say the word. If they can’t, it’s a clone. Hang up immediately.
- The “Call Back” Rule: Never authorize a payment on an incoming call. Always hang up and call the person back on their saved number.
- Voice Privacy: Be mindful of “Public Audio.” If you are a high-net-worth individual or a business owner, consider using “Voice Masking” or keeping your personal social media profiles private.
The Future: Can We Ever Trust Again?
As we move toward 2030, the “Identity Crisis” will only deepen. We are entering a world where “Proof of Personhood” will become the most valuable currency. We might soon need blockchain-verified “Voice Signatures” just to leave a voicemail.
AI isn’t the villain here it’s just a mirror of human intent. The same technology that allows a paralyzed person to speak again is being used to empty bank accounts. The difference lies in Awareness.
Don’t let your voice be the reason your bank account goes to zero. Stay skeptical, stay loud about security, and most importantly, stay human.





Leave a Reply