In the world of modern development, speed is often prioritized over safety. We live in the era of “Ship it fast, fix it later.” But there is one mistake that doesn’t give you a second chance: Hardcoding an API Key. What looks like a harmless 32-character string sitting in your config.js or main.py is actually a master key to your digital kingdom. In this “autopsy,” we will dissect how a single line of code can lead to a financial and security catastrophe, and why 2026 is seeing a record number of “Secret Leaks.”
The 3:00 AM Notification: A Human Reflection

“The Moment Your Heart Drops: When GitHub tells you that you’ve been pwned.”
Ask any senior developer, and they likely have a “horror story” from their junior days. I remember mine clearly. I was tired, rushing to meet a deadline, and I pushed a small update to a public repo. I forgot that I had temporarily pasted my AWS root key into the script for testing—telling myself I’d “remove it before the final merge.”
I didn’t.
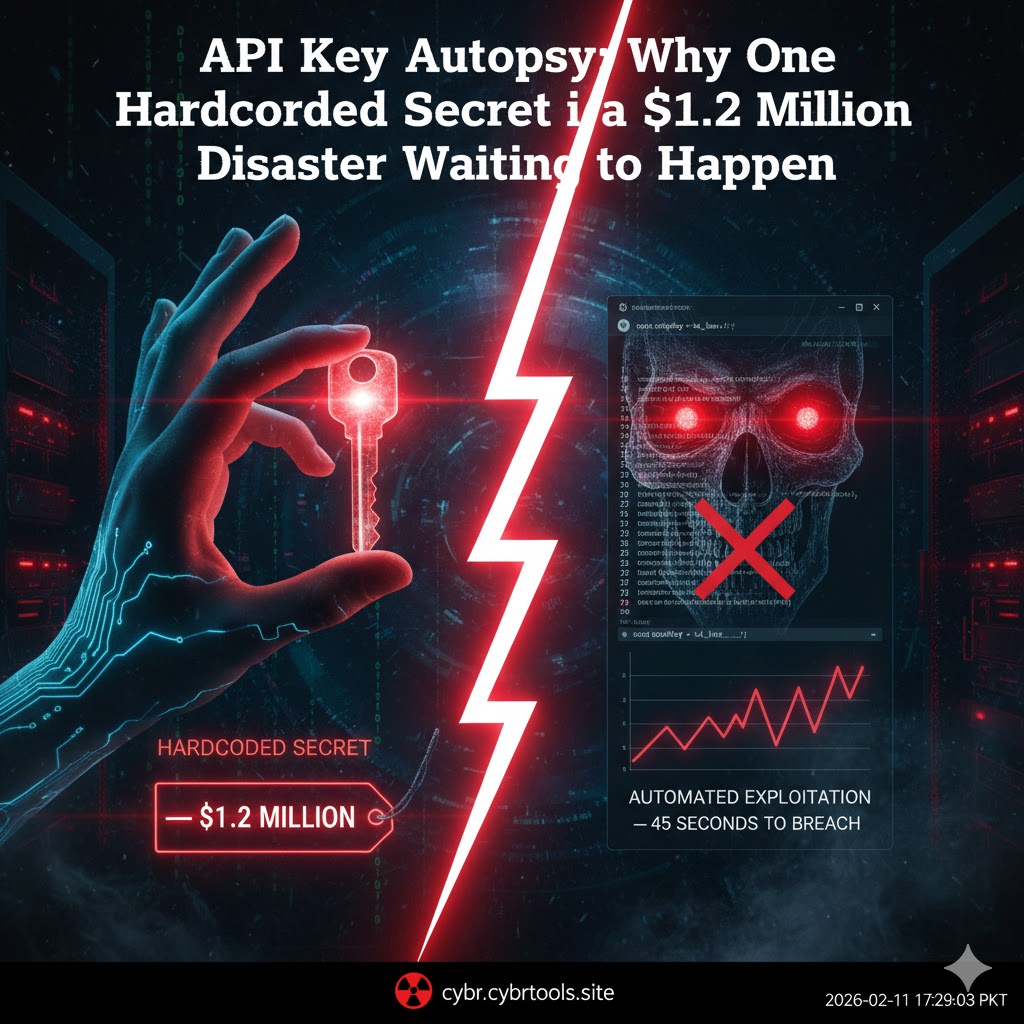
Within 45 seconds not minutes, seconds my phone started blowing up with automated alerts. AWS had detected the leak, but by the time I revoked the key, botnets had already intercepted the commit. These aren’t humans sitting at desks; they are high-speed scripts designed to instantly exploit found credentials. By the time I logged into my dashboard, those bots had already spun up 50 high-powered GPU instances in five different regions. The total damage in under 5 minutes? $4,200. That was my “Developer’s Baptism by Fire.” It wasn’t just about the money; it was the realization that in the digital wild west, bots are faster than your brain.
The Anatomy of a Leak: How Automated Bots Harvest Your Mistakes

“Why Botnets love your ‘Testing’ scripts more than you do.”
How does a leak actually happen? It’s rarely a targeted hack by a masked individual. It’s an automated harvest. The process is terrifyingly efficient:
- The Commit: You push code containing a secret (OpenAI key, Stripe secret, or AWS credentials). Perhaps you thought the repository was private, or you forgot that
.gitignoredoesn’t work for files already tracked by Git. - The Scanner: Thousands of bots are constantly “tailing” the GitHub public events stream. They don’t read your code to understand its logic; they use Regular Expressions (Regex) to scan for specific patterns that look like keys—usually strings starting with
sk_live_orAKIA.... - The Exploitation: The moment a key is found, it is automatically validated. If it’s a Stripe key, the bots try to process small refunds to test its validity; if it’s an AWS or Azure key, they immediately start crypto-mining or data exfiltration.
In 2026, the cost of a data breach has risen significantly. According to recent reports in Digital Utilities/Cyber News, the average cost of a secret leak for a mid-sized company now touches $1.2 Million. This isn’t just the bill from the cloud provider—it includes legal penalties, the cost of forensic audits, and the massive loss of customer trust that follows a public vulnerability.
The Mathematical Risk: Probability vs. Visibility Surface

“The Leak Equation: Calculating the surface area of your vulnerability.”
Your security risk isn’t just about the number of keys you have; it’s about their “Visibility Surface.” In 2026, we use a simple formula to calculate the potential for disaster:
$$Risk = \frac{(Number of Secrets \times Repo Visibility \times Permissions)}{Detection Time}$$
- Number of Secrets: Every third-party integration adds a potential point of failure.
- Repo Visibility: Public repos are a 10/10 risk, but internal private repos are often 5/10 because “Insider Threats” or compromised employee accounts are common.
- Permissions: A key with “Root” or “Admin” access is 100x more dangerous than a “Read-Only” key.
- Detection Time: This is the most critical variable. If your detection time is high (meaning you don’t use automated secret scanning), your risk grows exponentially every second. This is why tools found in our Security Tools section are no longer optional—they are your only line of defense against the speed of light.
Hardcoding: The “Technical Debt” That Never Ends
“Why ‘I’ll fix it later’ is the most expensive phrase in programming.”
Hardcoding is a symptom of Technical Debt. You tell yourself you’ll move it to an environment variable later, but as the project grows, that key gets buried deep within the logic. You might rename the variable or move the file, but the secret remains.
The Ripple Effect is Permanent:
- The Git History Trap: This is what most developers forget. Even if you delete the key in a new commit and push it, the secret stays in your
.gitfolder history. Anyone who clones your repo can simply checkout an older commit and find the key. You haven’t deleted the secret; you’ve just hidden it under a rug in a house with glass walls. - Developer Trust & Culture: A leaked key can ruin a team’s reputation. It signals to investors, clients, and senior management that your internal security culture is weak. In 2026, companies aren’t just hiring people who can code; they are hiring people who can code securely.
2026 Strategy: How to “Secret-Proof” Your Career
“Beyond .env: Modern secret management for the utility-first developer.”
Static .env files are a massive improvement over hardcoding, but in 2026, the industry has moved even further. Here is the modern hierarchy of secret management that separates the amateurs from the pros:
- Level 1 (The Baseline): Use Environment Variables. Never, under any circumstances, push your
.envfile to version control. Use a.env.examplefile to show what variables are needed without including the actual values. - Level 2 (The Shield): Use Pre-commit Hooks. Tools like TruffleHog or GitGuardian can be installed locally. They scan your code before you hit the “Commit” button. If they find a secret, they block the commit, saving you from your own forgetfulness.
- Level 3 (The Fortress): Use a Secret Vault. For production environments, your code should never “possess” the key. Instead, it should use a service like HashiCorp Vault, AWS Secrets Manager, or Azure Key Vault. Your application requests a temporary, short-lived token to perform a task, meaning even if a hacker breaches your server, they find a key that expires in 15 minutes.
The “Clean-Up” Protocol: Damage Control
“What to do when the damage is already done.”
If you realize you’ve leaked a key, don’t panic, but don’t just “delete” the line of code. Follow the Revoke-Rotate-Remediate protocol immediately:
- Revoke: Deactivate the key immediately from the provider’s dashboard. This is the only way to stop the bleeding.
- Rotate: Generate a new key. Do not reuse any part of the old one. Update your production environment using secure variables immediately.
- Remediate: You must scrub your entire Git history. Use a tool like BFG Repo-Cleaner or the
git-filter-repocommand. This “rewrites” your history to act as if the key was never there. If the repo is public, consider the data already stolen and change every password associated with that account.
Final Thoughts: The Cost of a Lesson
“Is your convenience worth a million-dollar invoice?”
API keys are the lifeblood of modern web tools. They allow our apps to talk, pay, and think. But treat them like a loaded weapon. Hardcoding is an amateur mistake that the 2026 landscape does not forgive.
In our pursuit of building the future, let’s not leave the door wide open. Build with logic, deploy with caution, and remember: The best place for an API key is anywhere except your code.





Leave a Reply